#Restaurante
Bienvenido a Nómada, la nueva propuesta gastronómica con la que la cocinera y primera ganadora de Top Chef, Begoña Rodrigo, te hará disfrutar de una nueva forma de comer. Te haremos perder el rumbo respecto a todo lo que hayas probado antes, en un viaje hacia la libertad en la cocina. En Nómada sólo encontrarás una frontera en nuestro recorrido, la temporalidad de los alimentos que se sentarán a tu mesa, llegados directamente de nuestro entorno más cercano para contribuir a una forma de cocinar más verde, saludable y sostenible.
Y como buen nómada, no sólo probarás nuestros platos, sino que serás parte de la travesía. Tú pones los límites de la experiencia. ¿Te atreves a jugar con fuego o con hielo?, ¿estás dispuesto a mirar la cocina con otros ojos y diseñar tu propio plato? Pues prepara tu pasaporte gastro y ven a dar una vuelta al mundo sin moverte de nuestro local. Y recuerda, el límite para este viaje sólo lo pones tú. O tu imaginación.
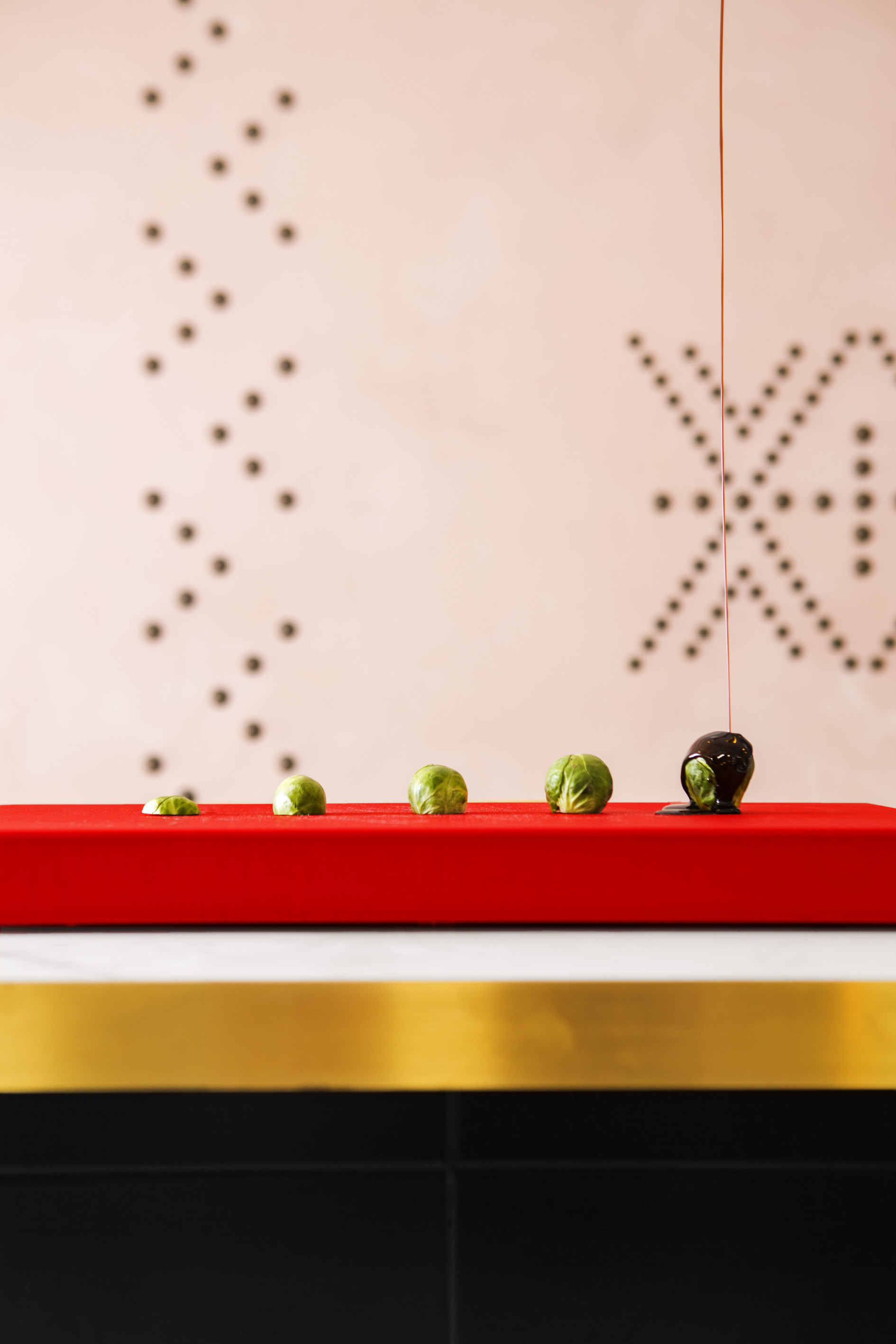
Cruza las puertas de Nómada y adéntrate en un viaje para tus sentidos a lo largo de XX metros cuadrados. El restaurante busca su inspiración en la naturaleza, sin perder ni un ápice de sofisticación. La idea del equipo liderado por Begoña Rodrigo es la de hacer sentir a sus huéspedes viajeros como en casa, sin renunciar a una cuidada decoración con la que dar un paseo por el mundo. Presidido por una imponente barra central de más de doce metros de largo, sobre la que podemos ver en directo cómo se cocina cada plato de la carta, cocineros y camareros conviven en un frenético servicio para que los más curiosos no pierdan detalle de todo lo que ocurre delante de sus ojos. En Nómada no queremos que nadie te cuente lo que pasa, sino que preferimos que seas protagonista de tu propia experiencia.
#La Carta
EL PICA PICA
Crujientes de arroz marino, camarón y guacamole
Bravas
Cornetto de foie
Taco de cochinita (ud.)
Ensaladilla
Croquetas caseras (ud.)
ENTRANTES
Mejillones curry verde
Pepito de conejo
Bao pato pekin (2 uds.)
Nuggets de manitas de cerdo y setas(4 uds.)
Brioche de pecho de ternera
Burrata (125g.), tomate valenciano y albahaca con tostas
Alcachofa, jamón y huevo frito (o algo así)
Causa limeña con sardinas ahumadas
Txipirones salteados con papaya thai (4 uds.)
Fish and chips
PRINCIPALES
“El Pescao” en su adobo
Calamar playa a la brasa y cítricos
Espeto de dorada y tabulé
Arroz basmati aromatizado con pulpitos encebollados
Chili crab y noodles
Lasaña de vaca y gamba con cebolla crispy
Dumpling de all i pebre con anguila ahumada (4 uds.)
Salmón a la brasa, benedictine y ensalada de espinacas
Hamburguesa goulash
Pastrami casero sandwich club
½ Pastrami
POSTRES
Nuestra tarta de Baileys y frutos rojos
Lima limón
Carrot cake
Trufón de chocolate
Pastel de chocolate caliente a nuestra manera
Mojito de fruta de la pasión y brocheta de fruta de temporada
LOS VERDES
Mejillones curry verde
Pepito de conejo
Bao pato pekin (2 uds.)
Nuggets de manitas de cerdo y setas (4 uds.)
Brioche de pecho de ternera
Burrata (125g.), tomate valenciano y albahaca con tostas
Alcachofa, jamón y huevo frito (o algo así)
Causa limeña con sardinas ahumadas
Txipirones salteados con papaya thai (4 uds.)
Fish and chips
LOS FUCSIAS
Nuestra tarta de Baileys y frutos rojos
Lima limón
Carrot cake
Trufón de chocolate
Pastel de chocolate caliente a nuestra manera
Mojito de fruta de la pasión y brocheta de fruta de temporada
LOS AZULES
“El Pescao” en su adobo
Calamar playa a la brasa y cítricos
Espeto de dorada y tabulé
Arroz basmati aromatizado con pulpitos encebollados
Chili crab y noodles
Lasaña de vaca y gamba con cebolla crispy
Dumpling de all i pebre con anguila ahumada (4 uds.)
Salmón a la brasa, benedictine y ensalada de espinacas
Hamburguesa goulash
Pastrami casero sandwich club
LOS VERDES
Mejillones curry verde
Pepito de conejo
Bao pato pekin (2 uds.)
Nuggets de manitas de cerdo y setas (4 uds.)
Brioche de pecho de ternera
Burrata (125g.), tomate valenciano y albahaca con tostas
Alcachofa, jamón y huevo frito (o algo así)
Causa limeña con sardinas ahumadas
Txipirones salteados con papaya thai (4 uds.)
Fish and chips
LOS AZULES
“El Pescao” en su adobo
Calamar playa a la brasa y cítricos
Espeto de dorada y tabulé
Arroz basmati aromatizado con pulpitos encebollados
Chili crab y noodles
Lasaña de vaca y gamba con cebolla crispy
Dumpling de all i pebre con anguila ahumada (4 uds.)
Salmón a la brasa, benedictine y ensalada de espinacas
Hamburguesa goulash
Pastrami casero sandwich club
LOS FUCSIAS
Nuestra tarta de Baileys y frutos rojos
Lima limón
Carrot cake
Trufón de chocolate
Pastel de chocolate caliente a nuestra manera
Mojito de fruta de la pasión y brocheta de fruta de temporada
#Los vinos
Cavas
Capracia
bodega vegalfaro: chardonnay macabeo
Luna
bodega murviedro uva: macabeo
Arts de luna
bodega murviedro uva: chardonnay
tantum ergo
bodega hispano suizas uva: chardonnay, pinot noir
Tantum ergo rosado
bodega hispano suizas uva: pinot noir
Raventos i blanc
bodega raventos i blanc uva: xarel.lo 50% macabeo 40%, perellada 10%
Gramona imperial
bodega gramona uva: chardonnay, xarel.lo, macabeo
Gramona 3 lustros
bodega gramona uva: xarel.lo macabeo
champagne y crêmant
Piollot grande reserve
bodega piollot uva: chardonnay, pinot noir, pinot meunier
Moineaux blanc de blancs
bodega moineaux uva: chardonnay
crêmant d’alsace
bodega kientz uva: Pinot blanc, auxerois
crêmant d’alsace rosé
bodega kientz uva: pinot noir
vinos blancos
d.o. utiel-requena
rebel.lia blanco
bodega vegalfaro uva: sauvignon blanc, chardonnay
mestizaje blanco
bodega mustiquillo uva: merserguera
pago de los balagueses chardonnay
bodega vegalfaro uva: chardonnay
d.o. valencia
beberas de copa de tu hermana
bodega fil.loxera cia.
blanc d’enguera
bodega enguera: Sauvignon blanc, chardonnay, viognier, verdil
Cullerot
bodega celler del roure: chardonnay, pedro ximenez, macabeo, verdil
Los almendros
bodegas uva: verdejo, sauvignon blanc
K-Naia
bodega naia uva: verdejo
monsalve
bodega
Belondrade y lurton
bodega belondrade y lurton
d.o. ribeiro
alaila
bodega goto de gomariz uva: treixadura
ALEMANIA
selbach-oster riesling trocken (seco!)
bodega selbach-oster uva: riesling
FRANCIA
les copines
sauvignon blanc, chardonnay, semillion blanc
kientz gewürztraminer
bodega kientz uva: gewürztraminer
kientz riesling petit vigne de d’emeline
bodega kientz uva: riesling
kientz pinot gris
bodega kientz uva: pinot gris
vinos tintos
vinos d.o. requena-utiel
los aves de paso
bodega viticultores lonecesario
lonecesario
bodega viticultores lonecesario
rebel.lia
bodega vegalfaro uva: bobal
basus
bodega hispano-suizas uva: bobal
finca terrerazo
bodega finca terrerazo uva: bobal
bobal viñas viejas
bodega murviero uva: bobal
murviedro colecion roble
bodega murviedro uva: bobal
murviedro colecion reserva
bodega murviedro uva: 40% tempranillo, 40% monastrell, 20% cabernet sauvignon
murviedro syrah
bodega murviedro uva: syrah
murviedro colecion reserva bobal
bodega murviedro uva: bobal
quincha corral
bodega mustiquillo uva: bobal
mestizaje
bodega mustiquillo uva: bobal, cabernet sauvignon, merlot,syrah, tempranillo
finca terrerazo
bodega mustiquillo uva: bobal
d.o. valencia
sentado sobre la bestia
bodega fil.loxera cia. uva:
safra
bodega celler del roure uva: mando, monastrell
Alcusses
bodega celler del roure uva: tempranillo tinta fina, cabernet sauvignon, syrah, monastrell
Parotet
bodegas celler del roure uva: monastrell, mando
Maduresa
bodega celler del roure uva: tinta fina, cabernet sauvignon, syrah, monastrell
almuvedre
bodega compañia de vinos telmo rodriguez uva: monastrell
d.o. rioja
el guia
bodega finca de la rica uva: tempranillo
el nomada
bodega finca de la rica uva: tempranillo
lindes de remelluri la bastida
bodega granja nuestra señora de remelluri uva: tempranillo
remelluri reserva
bodega granja nuestra señora de remelluri uva: tempranillo,garnacha, graciano
d.o. ribera del duero
denebola
bodega denebola uva: tinta fino
denebola crianza
bodega denebola uva: crianza
mauro
bodegas mauro uva: tinta fina
#Nómadas
BEGOÑA RODRIGO
Xirivella 1975
Llegó al mundo de la cocina casi por necesidad. “Yo no he decidido ser cocinera. La vida lo ha hecho por mí”, asegura. Su dilatada experiencia en la cocina no le viene de familia, ni de tradición. De hecho, cuando era pequeña, a la señorita petit suisse (como la llamaban en casa porque sólo comía yogures) ni siquiera le gustaba comer. Ingeniera industrial de formación (le falta el proyecto para acabar la carrera), antes de meterse en harina abrió dos exitosos negocios de pan y dulces en Valencia a los 18 años antes de poner rumbo a Holanda. A Amsterdam llegó de vacaciones el verano en que cumplió 20 años, pero a los dos meses volvió para quedarse ocho años. Antes de ser cocinera limpió habitaciones de hotel y poco a poco consiguió un puesto en su particular escuela de hostelería, la cocina del Amsterdarm Marriot. Después las despensas de Mozambique, Tailandia, Estados Unidos o Londres han conformado su particular carta de sabores. Todo ellos, sin perder ni un ápice de sus raíces valencianas. Pero las casualides del destino la llevaron de vuelta a casa para ayudar a su hermana Ruth en la inauguración del que iba a ser su restaurante. Un local en la calle Séneca de Valencia que no terminó de cuajar y que hoy en día es La Salita, el restaurante gastronómico de Begoña. Fue un 2 de noviembre de 2005 y ya ha cumplido más de una década de éxitos. En La Salita experimenta con los productos más locales para darles un concepto global. Para ello, controla todo el proceso de producción de los vegetales desde su cultivo.
JESÚS ERES
1981 / Jefe de Sala
Amanecí un 7 de Noviembre del 81. Licenciado en Derecho, aunque no he llegado a ejercer nunca como abogado. Soy ferroviario de vocación y, de hecho, he trabajado como maquinista durante mogollón de años. Hasta que hace unos meses un tuit hizo que cambiara mi rumbo laboral. Siempre he sido un disfrutón de la gastronomía y para mí es una oportunidad increíble afrontar este reto en Nómada y sobre todo, ha sido un honor haber formado parte del equipo de sala de La Salita. Como decía, formo parte del equipo de sala del Restaurante Nómada y me encargo del trato con los clientes y de ayudarles a tener la mejor experiencia posible en el restaurante. Me puedo definir como enamorado de los trenes y de los buenos momentos sentado a la mesa compartiendo buena comida y mejor conversación. Viajero empedernido y repostero ocasional.
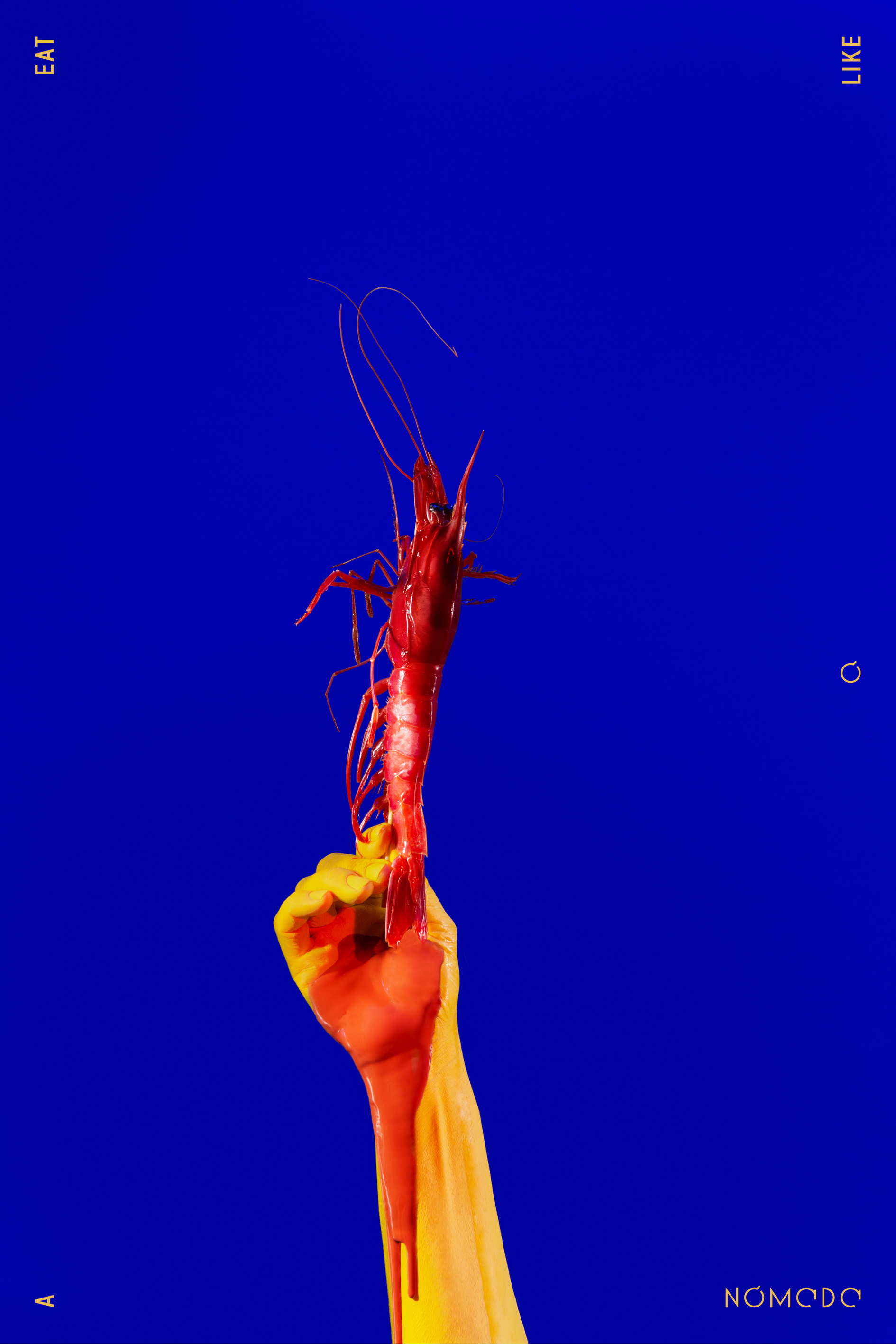
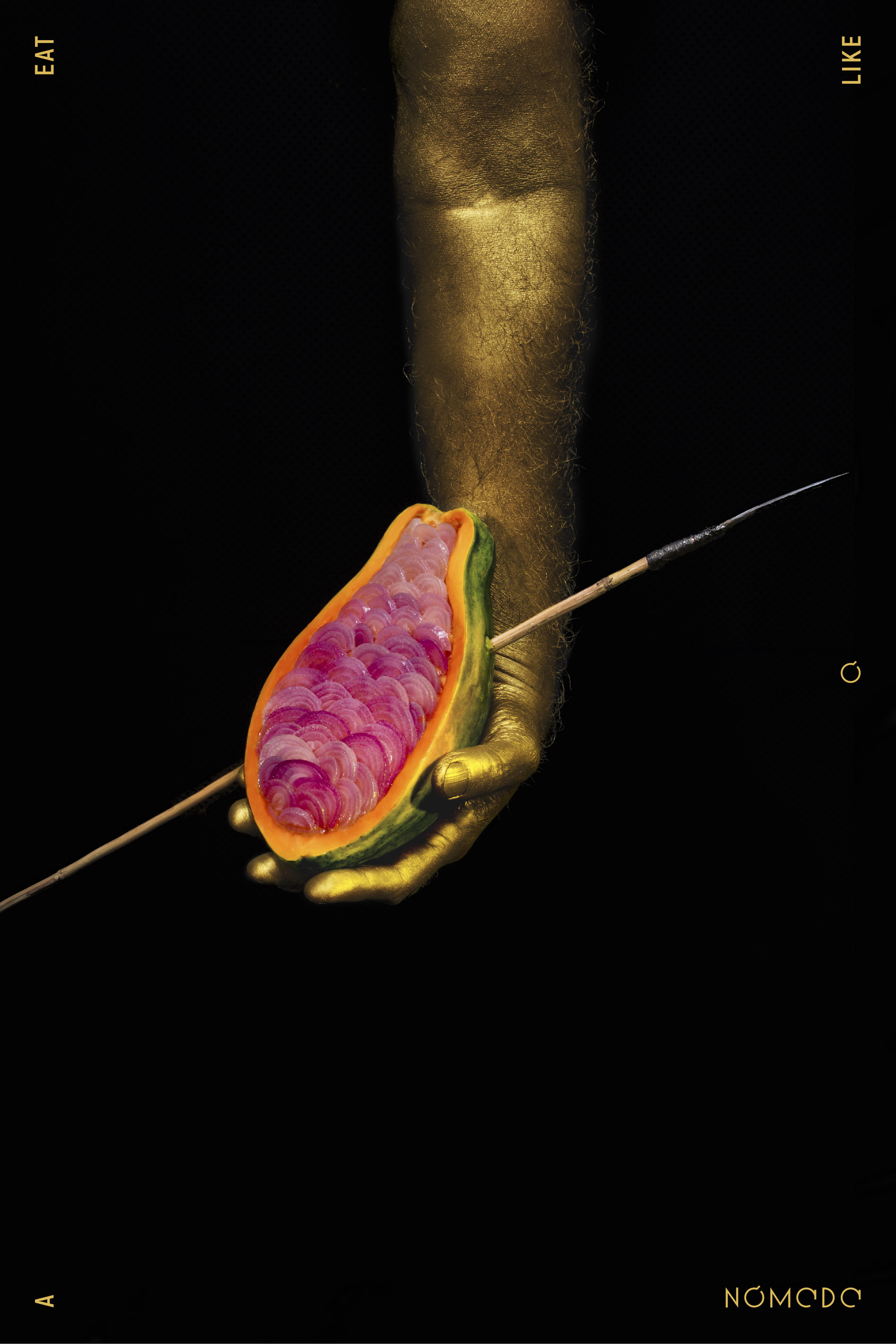
#EAT LIKE A NOMADAS
REGALA
UNA
EXPERIENCIA
NÓMADA
Escríbenos un mail a nomadaregalo@gmail.com con el importe que deseas regalar (importe mínimo 40€), el nombre del receptor del regalo y el justificante del banco y te enviaremos un mail con un cheque regalo Nómada para consumo en el restaurante.
El Cheque regalo tiene un año de duración desde el día de expedición.
Cuando deseen utilizarlo, solo necesitan llamar efectuar una reserva e indicar el numero de cheque regalo Nómada.
Cta de ingreso
ES23 3058 2292 1127 2000 5746
(El cheque regalo no es reembolsable por efectivo)
#CONTACTO
DIRECCIÓN
Centro Comercial Bonaire
Km 345 Carretera de Madrid
Primera Planta, Local 7
46960 Aldaia – VALENCIA
RESERVAS
T 961061834
hello@eatlikeanomada.com
TRABAJA CON NÓMADAS
Si quieres formar parte del equipo o hacer un Stage con nosotros escribe a nomadamep@gmail.com
© C A R M E L A . W O R K – Photo y Video